Block-chains are secure, encrypted distributed and decentralized databases.
These systems don’t have a centralized control. The ultimate objective of such distributed network is to achieve more equality, security and freedom in peer to peer sharing of resources.
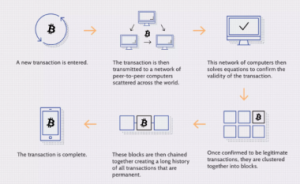
Image source: https://www.investopedia.com/terms/b/blockchain.asp. By Luke Conway
Block-Chains And Data Organization:
A block-chain is (in the majority of times) a distributed and public digital ledger consisting of multiple small archives of information, called blocks. In other words, it’s a specific type of database. As new data comes in, a new block is taken by it. Once this block is filled, it will be attached to the rest of them, creating the so called chain. This is accomplished by mining, in nodes with the specific job of validating transactions: these will be later added to the block they are “building”, and then broadcast the completed block to other nodes.
A block-chain database is used to keep track of transactions across many computers so that an involved block can’t be altered without doing so with all the previous ones in the chain.
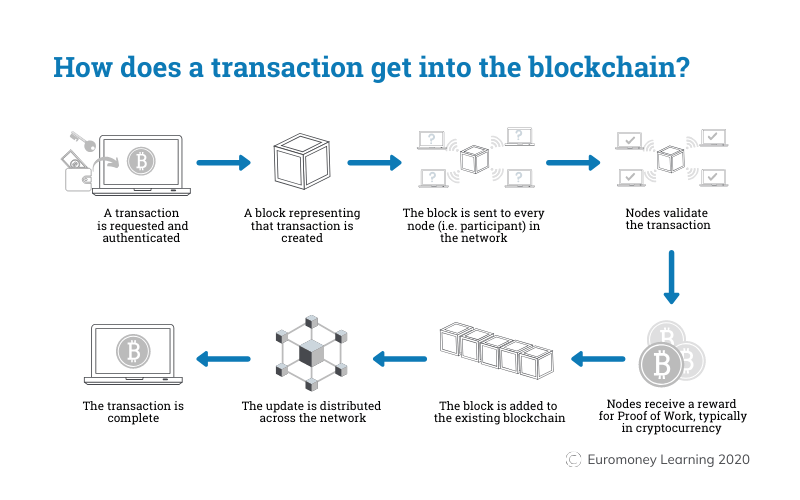
Image source:https://www.euromoney.com/learning/blockchain-explained/how-transactions-get-into-the-blockchain
Why Block-Chains?
A block-chain database is run using a p2p network and a dedicated server for keeping track of the creation and modification time of documents or data. It can be seen as a protected protocol (set of rules) for information exchanges. It can be used for different types of information, so it could be naïve to think its only purpose would be that of giving and taking money, as in the Bitcoin case.
Due to its blocks organization, a block-chain lacks centralized points of vulnerability that malicious actors can exploit. It is indeed a distributed network, which means that data is spread across more than one computer. Nodes (computers) are dependent from each other and oftentimes communicate through encrypted communication.
The ultimate objective of a distributed network is to achieve a secure sharing of resources that matters to each of the nodes. In Bitcoin’s case that would be value/money and the safer the transaction, the happier the person behind the node.
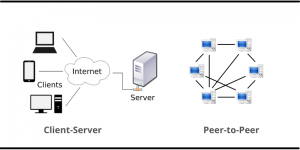
Client server vs p2p network showing data flow directions and possible paths.
Image source:https://www.networkstraining.com/peer-to-peer-vs-client-server-network/
A Decentralized System:
Having their platform information spread across multiple machines, decentralized databases are virtually invulnerable to external hacks. There is no pivot in the arrangement, no weak point to exploit, communication usually undergoes strong encryption and a copy of the chain is owned by every user in the network.
If a hacker wants to alter the block-chain for malicious intents, his copy of the modified chain wouldn’t align with everyone else’s, leading to a failed attempt. In order to actually change the chain, the hacker would need to do so in at least 51% of the remaining nodes requiring huge amounts of money, resources and time. In other words, the chance of a virtual attack succeeding is close to none.
It sounds very good so far and there are decidedly strong pros in this scheme, but we’re far away from saying this is a perfect system. It’s really up to the needs of the people who are in it and no matter what they want, everyone will have to compromise in order to be part of it.
Nevertheless, decentralized systems also mean: no ownership (so it’s difficult to maintain), data is frequently only added through community consensus, (nobody owns the data and everyone owns the data), performance is not prioritized but security is (a Bitcoin transaction verification is super secure, but it can take up to 20 minutes).
Growth of a decentralized block-chain easily leads to centralization as the hardware resources needed to process growing amounts of data become more and more expensive.
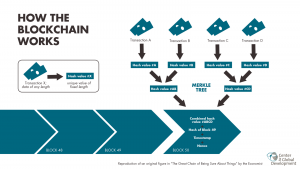
Image source: https://commons.wikimedia.org/wiki/File:Blockchain_workflow.png
Is This System Worth It?
Block-chains and decentralized systems are always worth it if the people who are in this system agree to the fact that they want security more than anything else. It really comes down to the needs of the peers and, looking at the Bitcoin example, seems to be the most fitting database type out there.
It is also utilized in a number of companies and/or agencies that will give up privacy in professional matters in order to keep its data safe, and it’s completely understandable.
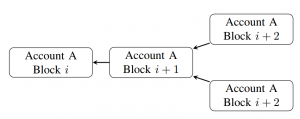
Image source: https://commons.wikimedia.org/wiki/File:Account-Chain_Fork_Structure.png
Info source:
https://aws.amazon.com/blockchain/decentralization-in-blockchain/
https://www.investopedia.com/terms/b/blockchain.asp
https://www.sciencedirect.com/science/article/abs/pii/S2352673419300824
